2.6 million ransomware attacks in Q1 2023: Why India is now a prime target for cyber threats
- InduQin
- Jan 10, 2024
- 7 min read
There has been a data breach.
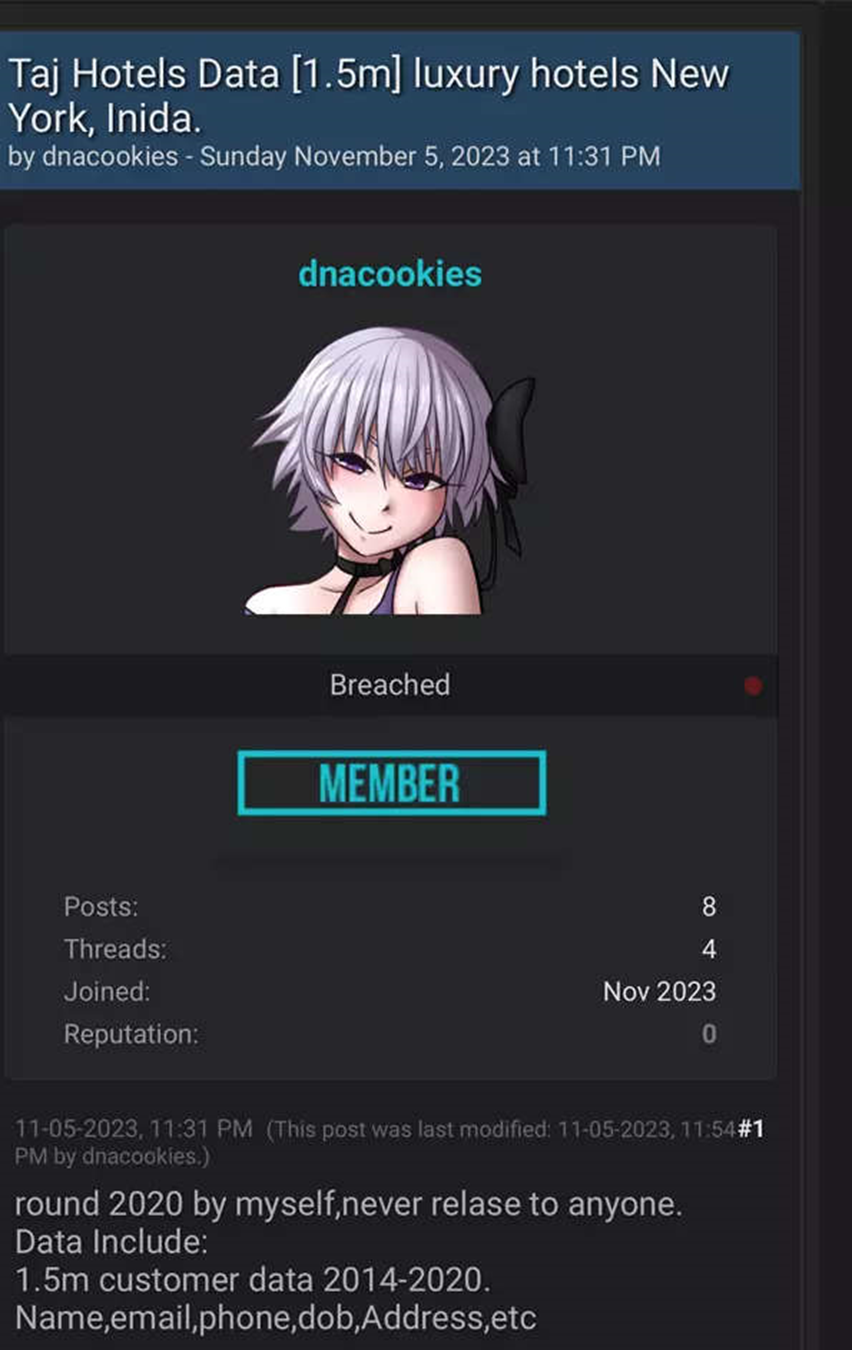
According to reports, 1.5 million customers' personal information was compromised in November by Taj Hotels. The hacker behind the Dark Web breach, who goes by the handle Dnacookies, offered to sell the sensitive information—which included names, addresses, emails, and membership IDs—for USD5,000. He also published some sample data.
Then, as reported by TechCrunch, the National Aerospace Laboratories (NAL) was the next target of the LockBit ransomware group, who threatened to release the organization's data unless the "unspecified ransom" was paid.
Having said that, ransomware attacks are unfortunately not uncommon, particularly this year.
With 2.6 million ransomware attacks in Q1 2023—a 133% increase over the previous six months—India joined the exclusive club of countries hit hard by ransomware.
Even more concerning than the sheer number of attacks is the fact that a staggering 73% of the reported Indian enterprises are still vulnerable, with an average ransom demand exceeding USD1.2 million. In a recent analysis, Arete—a worldwide cyber risk management company—found that this average rises to USD20 million.
This year, healthcare (28%), education (23%), and finance (20%) were the most impacted sectors in India, according to a survey by Sophos, a UK-based security software and hardware company. This is a big change from the main targets for 2022, which were the government (18%), healthcare (20%), and finance (22%).
Why has India suddenly become a hotspot for cybercriminals, and what caused this spike?
Information Storing Clouds
Although the claimed breach at the Taj Hotel is relatively new, there has been no shortage of breaches like this—as we saw earlier.
For the same, there are two main causes.
First, businesses are required to report security breaches to the Indian government's CERT-In (Computer Emergency Response Team) within six hours of discovering them.
The success of software-heavy, asset-light disruptive business models like AirBnB has forced traditional companies to consider inorganic strategies or seek out third parties to build their tech stack, according to Pankit Desai, founder of the cybersecurity platform Sequretek.
"This could lead to security holes," he cautioned.
There are further worries as well. A high rate of employee turnover is common in the hospitality industry. Problems with institutional memory, training capabilities, and system and process awareness arise when there is a lot of turnover. Someone can come in if you break only one or two of the many factors you have. The amount of damage that technology can avert is, alas, limited," Desai continued.
The threat actor may have compromised Taj's systems in 2020 or gained access to the data by an internal Taj employee mishandling the visitor records, according to a brief review by Sunny Nehra, founder of the digital forensics business Secure Your Hacks.
You can see a screenshot of Dnacookies's post here:
When sensitive information falls into the wrong hands, what may happen? Nehra has issued a stern warning about the scammers' use of convincing phishing attempts and impersonation.
Recent occurrences
The Cyber Bureau of Investigations (CBI) launched an investigation into the January hack on Solar Industries Limited (SIL). The investigation by the agency found that a threat actor going by the names of BlackCat or ALPHV had taken sensitive material from SIL's servers and was demanding a ransom of USD29.99 million (about INR24 crore) to keep it from being made public on the Dark Web. Indian national security was jeopardized when hackers started leaking data after the corporation refused to pay.
Some dark web monitoring platforms and forums have been keeping tabs on BlackCat or ALPHV and have stated that stolen data from the SIL attack is being sold on a continuous basis.
A number of cybersecurity companies have offered their opinions on the attack's technical details and the threat actor's methodology, such as CloudSEK and Group-IB.
According to Aarushi Koolwal of CloudSEK SVigil, a cybersecurity consultancy, BlackCat's toolset is all the time changing. "Thus, we are unable to confirm the exact method by which Solar Industries was compromised."
She does note, however, that "ALPHV was a former member of the REvil group (Russia-based private ransomware-as-a-service (RaaS) operation)," which she interprets as meaning that the BlackCat ransomware gang is likely linked to REvil. Therefore, this is a major assault on India's essential infrastructure.
However, the amount of data still available for purchase on the Dark Web makes this occurrence seem insignificant.
There was an attempt to sell a database in 2021 that included the Aadhaar numbers, names, residences, and phone numbers of more than 100 million people in India.
The next year, a data breach exposed the private details of more than 200 million Indians, including celebrities and public figures. A big Indian telecom corporation was allegedly the source of the data hack. At the same time, information about more than half a million Indian bank accounts was exposed on the underground network. Account numbers, routing information, and current balances were all included of the data set.
A new ransomware variant known as "LockBit 3.0" was aimed at Indian companies, according to CERT-In's warning this year.
Ransomware from the LockBit group accounts for 13% of all attacks in India, according to encryption tool NordLocker. Among these, publicly traded corporations in India are the focus of 21% of attacks.
A number of well-known corporations have been attacked by LockBit in recent months. Notable Taiwanese chipmaker TSMC, British postal and courier service Royal Mail, and large pharmaceutical business Granules India are among its recent victims. In previous years, LockBit has also targeted organizations including the California finance department and the Los Angeles housing authority.
Ransomware businesses have flourished on the Dark Web, giving attackers easy access to the resources they need to launch assaults. Worldwide, especially in India, ransomware assaults have been on the rise due to this increased accessibility.
The Spike
Some patterns have emerged from the most recent wave of ransomware assaults on Indian companies. It is worth mentioning that the healthcare, energy, and financial industries are the targets of attackers' attention.
According to Karmesh Gupta, CEO and co-founder of WiJungle, these attacks have become more complex over time, with an emphasis on the use of double extortion tactics. In this tactic, material is encrypted and then threatened to be released unless a ransom is paid. It is becoming more difficult to trace and recover ransommonies, as Gupta points out, because ransomware criminals are increasingly inclined towards cryptocurrency payments.
"According to Sundar Balasubramanian, managing director of Check Point Software Technologies India & SAARC, "there has been a significant increase in the frequency of ransomware attacks, with cybercriminals being able to remain anonymous thanks to the pivotal shift towards untraceable Bitcoin transactions." Balasubramanian explains that in the beginning, ransom demands were traced through cash or money orders sent to identifiable post office boxes linked to individuals.
As of this writing in 2023, one out of every thirty-four organizations around the globe has been the target of an attempted ransomware assault, according to research from CheckPoint. This is a 4% rise over the same time last year. It was slightly lower than the global average but still showing growth, affecting 1 out of 20 organizations across Asia Pacific.
Ransomware attacks are becoming more common in India because to a lack of understanding and proper cybersecurity safeguards by many organizations, especially smaller enterprises and government bodies. Some examples of this include using insecure software, not teaching employees strong password practices, and not keeping software up-to-date.
The aforementioned Sophos data shows that in 2023, the most common reasons for ransomware attacks in India were exploited vulnerabilities (35% of the total) and compromised credentials (33% of the total), which is a worrying trend that is hampering cybersecurity initiatives.
Also problematic is the absence of legislative protections and the companies' reactions to the attacks. According to an anonymous cybersecurity researcher, the initial reaction from firms is the same: that nothing is wrong and that no important information was obtained.
The sophistication of assaults has increased with the rise of AI and automation. Businesses should raise awareness among workers and improve security measures, but they should also notify customers and users of security breaches and take responsibility for them, he said.
The fact that ransomware most often targets email and PDF files is, according to Huzefa Motiwala, Director of Systems Engineering for Palo Alto Networks in India and SAARC, a major factor in the virus's persistence. According to Palo Alto Networks, a large percentage of consumers have no idea that malicious software could be sent using this particular file format. This is in light of the fact that research has shown that PDFs may be responsible for the delivery of as much as 66% of viruses. This highlights an important point that CISOs should convey throughout their organizations this year: use caution when dealing with PDFs.
What makes India so special?
India is rapidly enhancing its company and consumer connections through the use of more digital methods, which is good for the economy. Cyber dangers including as ransomware attacks, credential theft, and supply chain breaches are on the rise due to the increasing digitization of everything. Bad actors have more opportunities to get in as firms utilize more linked digital systems to improve consumer experiences and streamline operations.
"About half a year ago, the average ransomware demand in India was zero, and now it's somewhere around USD200,000 per incident," Gupta of WiJungle shared.
Furthermore, he went on to say, "This increase places a substantial financial burden on businesses, particularly small and medium-sized enterprises, which may struggle to meet such demands."
Cybercriminals target India because of the country's booming economy and rising Internet usage in an effort to extort money from businesses and individuals there. The possibility of financial gain is an undeniable motivator for ransomware assaults.
Another perspective, though, emerges.
India has cordial ties with powerful nations like the United States, Russia, and China, and it also has a significant geopolitical footprint. Yihao Lim, Mandiant JAPAC Lead Threat Intelligence Advisor at Google Cloud, warned that this would put India at risk of more espionage and hacktivism assaults as a result of developing global conflicts.
Many Indian organizations do not have the strong cybersecurity procedures needed to successfully protect themselves against ransomware attacks, as Koolwal pointed out, and India's cybersecurity capabilities are still evolving.
Cyber espionage, cybercrime, hacktivism, and information operations have been on the rise throughout past elections and are expected to persist in the future year, according to the Google Cloud Cybersecurity Forecast 2024, which was just presented by Mandiant.
Addendum: "The general trends noticed in India align with those of other global emerging economies," Lim reiterated.
The Final Note
More stringent cybersecurity measures are required as India solidifies its place as one of the top nations most vulnerable to ransomware attacks.
The prevalence of these attacks highlights the critical need for proactive defenses and robust preparation plans across all industries.
Preparedness is the key for every organization, whether it's NAL, Taj, SIL, or any other, until a well-planned strike halts all activities.
Get in your saddles and make sure you have backups!







Comments